Bring your company's cyber security stance in compliance with industry standards.
Open Source Intelligence Cyber Risk Assessments Insider Threats Training Incident Response Pentesting Staff Augmentation
Cyberattacks not only disrupt the digital life of corporations but can also put companies completely out of business. Every company, regardless of its size and industry, is facing IT risks on a daily basis. Your company will not be an exception to cyber threats until you make cyber security risk assessments a regular part of your work routine. Regular cyber risk assessments help detect vulnerabilities so that your business is armed to build timely and effective defense against any cyber threat that may affect your business now and in the future.
Why You Need Cyber Security Risk Assessment Services
Each business is a potential or active target of cyber criminals, yet most executive teams do not recognize this threat and do not take cyber risks seriously until a breach has occurred.
Each business requires an individual approach in achieving cyber security maturity.
Most businesses are bound to be compliant with various cyber security standards; these standards change, and their number grows.
Achieving cyber security maturity with in-house resources can be complicated and costly due to a shortage of experienced and skilled cyber security professionals in the market
How MBS Techservices Differs from Its Competition
MBS Techservices offers a set of services that address the needs of any business, at any stage of maturity and guides it through the full cycle. We help companies to achieve cyber security maturity and ensure that they stay on the correct course even when internal and external business environments change.
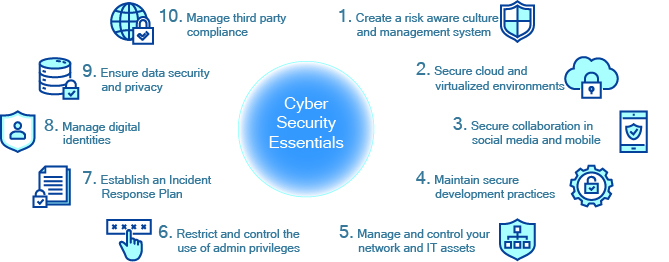
It is our view that a mature cyber security system is centered around 10 critical practices and capabilities, Cyber Security Essentials. MBS Techservices assesses each of these elements when conducting assessment and developing plans on achieving cyber security maturity. This model provides a framework for security investment and funding decisions.
Following assessment, our experts will help select best fitting software solutions and manage their installation, optimization, and long-term administration. MBS Tech offers a wide range of software solutions that can be installed to solve various security gaps.
MBS Techservices' Cyber Security Risk Assessment Services
Our services extend from tabletop awareness exercises for Executive Suite to ongoing progress monitoring. We are specialized in conducting structured cyber security risk assessments based on industry standards such as NIST, OSFI, ISO, NERC, etc.
Security Essentials Tabletop Exercise
The main purpose of this exercise is to educate your management team on the importance of Cyber Security Essentials for overall business wellbeing. We will discuss where the company’s current position is within the framework of the maturity model and compliance standards need to be adhered to for compliance. Upon completion, this exercise will turn your management team into cyber security fans and will ensure their support in budgeting cyber security solutions.
This workshop examines the corporate position in relation to each Cyber Security Essential. Conducted in collaboration with your cyber security / IT team, MBS Techservices will examine your current security capabilities, identify risks, and create a report card with findings and recommendations to guide your security program in ensuring it aligns with your business needs and maximizes your security investment. This workshop can be conducted as a bridge to a comprehensive Enterprise Maturity Assessment study.
Enterprise Maturity Assessment
This is a detailed examination of corporate cyber security procedures, processes, and practices, as well as tools and solutions. Our team will interview your staff, review all IT environments, security policies, processes, standards, incident response plans, data flow diagrams, configurations, documentation describing current controls and their maturity. We will run a comparative analysis against the industry-accepted standards and guidelines (e.g., COBIT, NIST CSF, NIST 800-53, ISO/IEC 27001 and 27002, etc.), which are relevant to your business, prepare gap analysis, develop evaluation ratings and recommendations for achieving full compliance.
Health Check / Environment Scans
This service is designed as follow-ups to the Maturity Assessment service or Security Essentials Workshop. Periodical reviews of the corporate progress in achieving the full maturity will ensure the security program aligns with business objectives and remains in sync with the changing external threat environment.
Get a Consultation on Cyber Security Risk Assessments
Contact us to inquire about the types of compliance assessments we can provide to your business.